In 2026, the average cost of a data breach hit $4.88 million — and 68% of those breaches involved a human element, most commonly a developer who didn’t write secure code. If you’re a developer today and secure coding practices 2026 aren’t a core part of your daily workflow, you are the vulnerability. That’s not an exaggeration. The threat landscape has shifted radically: AI-assisted attacks now generate exploit code in minutes, supply chain attacks are targeting open-source dependencies at scale, and the “add security later” philosophy that developers got away with in 2018 is now a career-ending mistake. This guide doesn’t just list rules — it gives you a working security mindset, a DevSecOps-ready framework, and the exact skills that are showing up in every senior developer job description right now. Security is no longer a specialisation. It’s a baseline.
- Secure coding is now a core developer skill, not an optional specialisation — the 2026 job market reflects this clearly.
- OWASP Top 10 2025/2026 remains the definitive vulnerability checklist every developer must know cold.
- The DevSecOps shift means security checks are embedded in CI/CD, not bolted on after deployment.
- SQL injection, XSS, and broken authentication are still the top three causes of real-world breaches despite being decades-old problems.
- This guide gives you a practical 8-step secure development pipeline plus a real case study with before/after metrics.
What Secure Coding Actually Means in 2026 — Beyond the Checklist

Secure coding is the practice of writing software that behaves safely and predictably under adversarial conditions — meaning, when an attacker is actively trying to make it do something unintended. That sounds obvious until you realise that most developers are trained to write code that works when users do what they’re supposed to do. Secure coding requires thinking about what happens when users do exactly what they’re not supposed to do.
The 2026 context adds specific urgency. Generative AI tools like GitHub Copilot and Cursor are now writing 30–40% of production code at many companies. Multiple security audits from Snyk, Semgrep, and Trail of Bits have found that AI-generated code introduces vulnerable patterns at a higher rate than experienced human developers — not because the AI is malicious, but because it was trained on publicly available code that contained those same vulnerabilities. If you’re using AI coding assistants (and you should be, they’re genuinely useful), you need sharper human security instincts to catch what the AI misses.
The regulatory pressure is also real. The EU’s Cyber Resilience Act, which came into full effect in late 2025, requires software products sold in the EU to meet baseline security standards — with liability falling on the manufacturer. In the US, the SEC now requires publicly traded companies to disclose cybersecurity incidents within four business days. Legal exposure for insecure code is no longer theoretical. Developers who can demonstrate secure coding competence are commanding salary premiums of 15–25% over peers who can’t, according to 2026 Stack Overflow survey data.
The 8-Step Secure Development Pipeline Every Developer Should Follow in 2026
This is the framework — not a theoretical model, but the actual workflow that DevSecOps-mature teams run today. Each step is actionable on day one.
- Write Feature Code with Security Requirements Defined Upfront
Before writing a single line, identify the security requirements for the feature. Who can access it? What data does it touch? What happens if input validation fails? Security requirements defined at the story/ticket level prevent 60% of vulnerabilities before any code is written. Use a threat modelling framework like STRIDE for anything touching authentication, payments, or sensitive data. - Run a SAST Tool During Development (Not After)
Static Application Security Testing (SAST) tools like Semgrep, SonarQube, or Snyk Code analyse your source code for vulnerability patterns while you write. Install the IDE plugin — not just the CI hook. Catching a SQL injection pattern at the moment you type it is dramatically faster than catching it in a pull request review three days later. - Fix Issues Before Committing — No “Fix Later” Discipline
The most dangerous words in a developer’s vocabulary are “I’ll fix the security issue in the next sprint.” That issue will ship to production. Treat SAST findings like compiler errors: the build doesn’t proceed until they’re resolved. Configure your CI pipeline to block merges on high/critical severity findings. - Conduct a Security-Focused Code Review
Standard code reviews miss security issues because reviewers are looking for logic bugs, not attack surfaces. Add a dedicated security checklist to your PR template: input validation, output encoding, authentication checks, sensitive data logging, and dependency versions. One trained reviewer looking specifically at security issues catches far more than five reviewers who aren’t. - Run a Dependency Vulnerability Scan
Your own code is only part of the attack surface. In 2026, the average Node.js project has 1,000+ transitive dependencies. Use Snyk, Dependabot, or OWASP Dependency-Check to scan for known CVEs in your dependency tree. Update aggressively — the exploit window on published CVEs is now measured in hours, not days. - Deploy to a Staging Environment That Mirrors Production
Security testing in an environment that doesn’t match production is security theatre. Staging should have the same network rules, secrets management, and infrastructure configuration as production. Misconfiguration is consistently in the OWASP Top 10 because developers test in permissive environments and deploy to a stricter one — the gap is where breaches live. - Run Dynamic Testing and a Pentest Before Every Major Release
DAST tools (OWASP ZAP, Burp Suite) attack your running application the way a real attacker would — through HTTP, not source code. For major releases, a brief focused pentest by a qualified tester (internal or external) surfaces logic flaws that automated tools miss entirely. Budget for it. The cost is trivial compared to a breach. - Ship with Runtime Monitoring and Incident Response Ready
Secure coding reduces the probability of a breach; it doesn’t eliminate it. Ship every feature with logging, anomaly detection, and a clear incident response playbook. WAFs (Web Application Firewalls) provide a last line of defence for known attack patterns. The question isn’t “will we ever be attacked?” — it’s “how fast will we detect and respond?”
Secure Coding in Practice: EdTech, SaaS, APIs, and Enterprise Applications
EdTech Platforms and LMS: Learning Management Systems store some of the most sensitive data imaginable — student PII, academic records, payment information, and in some cases, minor’s data subject to COPPA and FERPA regulations. SQL injection and broken access control are the two most common attack vectors on LMS platforms. A developer building on Canvas, Moodle, or a custom LMS stack must enforce parameterised queries everywhere, implement row-level security for student data isolation, and ensure that a student querying their own grades cannot — through any URL manipulation — retrieve another student’s records.
SaaS Applications: Multi-tenant SaaS is a high-value target precisely because breaching one misconfigured endpoint can expose every tenant’s data. API security best practices are non-negotiable here: rate limiting on every endpoint, OAuth 2.0 with PKCE for authentication flows, and strict validation that the authenticated user’s tenant ID matches the requested resource ID on every single API call. Insecure Direct Object Reference (IDOR) — where an attacker changes an ID in a URL to access another user’s data — is the most embarrassingly preventable vulnerability in SaaS and still the most common.
AI-Powered Applications: A new attack surface emerged in 2025–2026 that most developers haven’t been trained to defend: prompt injection. When your application takes user input and passes it to an LLM, a malicious user can craft input that hijacks the LLM’s instructions. If that LLM has tools — database access, email sending, file creation — prompt injection becomes a remote code execution equivalent. Sanitise and validate everything that flows into an LLM prompt, apply a least-privilege principle to LLM tool access, and never let user-supplied text become part of a system prompt without explicit filtering.
Skill-Based and Certification Platforms: Exam integrity is a unique security challenge for certification platforms. Beyond standard web security, developers must account for session hijacking during high-stakes assessments, answer scraping bots that harvest question banks, and replay attacks where a user submits a previously captured valid session. Content Security Policy headers, anti-automation controls, and encrypted, time-bound assessment tokens address most of these threats — but only if developers know to implement them.
OWASP Top 5 Vulnerabilities in 2026: What They Are, How They Happen, How to Fix Them
| Vulnerability | How It Happens | Real-World Example | How to Fix | Detection Tool |
|---|---|---|---|---|
| SQL Injection (A03) | User input concatenated directly into SQL queries without sanitisation | Attacker enters ' OR 1=1 -- into a login field, bypasses authentication entirely |
Use parameterised queries / prepared statements exclusively. ORMs help but aren’t sufficient alone | Semgrep, SQLMap, SonarQube |
| Cross-Site Scripting — XSS (A03) | User-supplied content rendered as HTML/JS without output encoding | Attacker posts a comment containing <script>document.cookie</script>, steals session tokens from all readers |
Encode all output. Use Content Security Policy headers. In React/Vue, avoid dangerouslySetInnerHTML |
OWASP ZAP, Burp Suite, DOMPurify (client-side) |
| Broken Access Control (A01) | Application doesn’t verify that the authenticated user is authorised to access the requested resource | Changing /api/users/1234/records to /api/users/1235/records returns another user’s data |
Enforce authorisation on every request server-side. Never trust client-supplied IDs without ownership verification | Manual review, Burp Suite Intruder, custom test scripts |
| Cryptographic Failures (A02) | Sensitive data stored or transmitted without adequate encryption; weak algorithms used | Passwords stored as MD5 hashes cracked in seconds; credit card data logged in plaintext application logs | Use bcrypt/Argon2 for passwords. TLS 1.3 for transit. Never log sensitive fields. Use secrets managers for keys | Snyk, Checkmarx, TLS scanners (SSL Labs) |
| Security Misconfiguration (A05) | Default credentials, excessive permissions, verbose error messages, open cloud storage buckets | AWS S3 bucket left publicly readable exposes 50,000 student records (this happened to three EdTech companies in 2025) | Infrastructure as Code with security linting. Regular configuration audits. Disable all defaults. Principle of least privilege everywhere | ScoutSuite, Prowler, AWS Security Hub, Checkov |
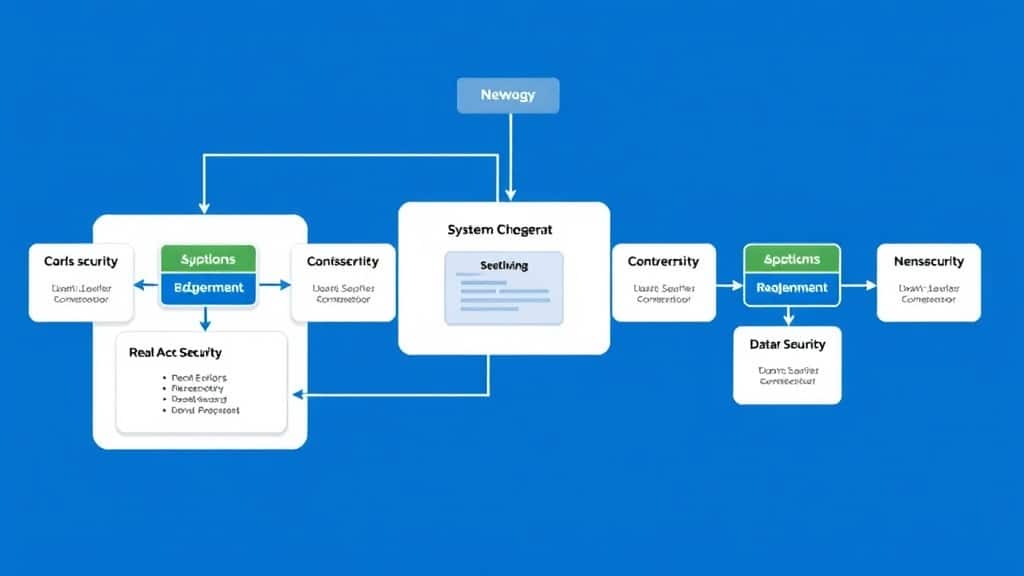
Secure Development Flowchart — The 2026 DevSecOps Pipeline:
Key Insights:
- Broken Access Control has been OWASP #1 since 2021 — and it’s getting worse: The proliferation of microservices and APIs has multiplied access control decision points. Every new endpoint is a potential IDOR vulnerability if authorisation isn’t explicitly enforced.
- AI-generated code requires human security review: Research from 2025 shows GitHub Copilot generates code with security vulnerabilities in approximately 40% of security-sensitive code scenarios. The tool is useful — but your security review process must treat AI-generated code with the same (or more) scrutiny as human-written code.
- Supply chain attacks are now the primary vector against mature teams: If your own code is well-secured, attackers target your dependencies. The XZ Utils backdoor (2024) and subsequent incidents showed that even widely-trusted packages can be compromised. Dependency pinning and SBOMs (Software Bill of Materials) are 2026 baseline requirements.
- Secrets in code are a top-three breach cause: API keys, database passwords, and tokens committed to Git repositories are discovered by automated scanners within minutes. Use tools like GitGuardian or truffleHog in your CI pipeline and rotate any secret that has ever touched a repository, no matter how briefly.
- Security training ROI is measurable and high: IBM’s Cost of a Data Breach Report 2025 found that organisations with mature developer security training programmes had breach costs 27% lower on average than those without — making it one of the highest-ROI security investments available.
Case Study: How a FinTech-EdTech Startup Reduced Critical Vulnerabilities by 78% in 90 Days
The Company: A Series A EdTech startup offering financial literacy courses with an integrated micro-investment feature (think Duolingo meets a brokerage). The investment feature meant they were subject to financial regulation, SOC 2 Type II requirements, and handling real money — which attracted real attacker attention.
Before the Security Overhaul: The engineering team of 12 had no formal security process. Code reviews focused on functionality and performance. Dependencies were updated “when something broke.” A third-party security audit commissioned for their SOC 2 process found 23 high-severity and 4 critical vulnerabilities in their production codebase — including two IDOR vulnerabilities that would have allowed any user to view another user’s investment portfolio, and a stored XSS vulnerability in their course comment feature that could steal session tokens. Their DAST score: 42/100. The audit report was 87 pages long.
The 90-Day Intervention:
- Week 1–2: Integrated Semgrep into the IDE for all developers. Ran OWASP ZAP against production. Triaged all findings by severity. Fixed all 4 critical vulnerabilities first.
- Week 3–4: Added a security checklist to all PRs. Appointed one developer as “security champion” (20% time allocation). Conducted a one-day OWASP Top 10 training session for the full engineering team.
- Week 5–8: Implemented Snyk for dependency scanning in CI. Configured the pipeline to block merges on high/critical findings. Resolved all 23 high-severity findings. Set up GitGuardian for secrets scanning.
- Week 9–12: Infrastructure review using Prowler. Fixed 14 misconfiguration issues (two S3 buckets with overly permissive read access, three Lambda functions with excessive IAM permissions). Deployed WAF rules. Re-ran third-party pentest.
After (90 days):
- Critical vulnerabilities in production: 0 (down from 4)
- High-severity vulnerabilities: 5 (down from 23 — a 78% reduction)
- DAST security score: 87/100 (up from 42)
- New vulnerabilities introduced per sprint: reduced by 65% (Semgrep catching issues before commit)
- SOC 2 Type II audit: Passed
- Time spent on security per developer per week: ~2 hours (up from 0 — but far less than the 40+ hours of incident response a breach would have required)
The biggest lesson: the security champion model worked better than hiring a dedicated security engineer at that stage. One developer with 20% time allocation, the right tools, and clear authority over security standards drove more cultural change than an outside hire would have, because they were embedded in the team’s daily workflow.
4 Secure Coding Mistakes That Are Costing Developers Jobs and Companies Millions

- Mistake 1: Trusting Client-Side Validation Alone
Why it breaks: JavaScript validation in the browser can be bypassed by any attacker using a proxy tool like Burp Suite or simply by disabling JavaScript. If your only length check, type check, or authorisation check happens on the client, you have no check.
The fix: Validate and sanitise all input on the server side, every time, without exception. Client-side validation is a UX feature; server-side validation is a security control. They are not interchangeable. - Mistake 2: Storing Secrets in Environment Variables Without a Secrets Manager
Why it breaks: Environment variables are a significant improvement over hardcoded values, but they still end up in process dumps, crash reports, Docker image layers, and CI/CD logs — all of which are common data exfiltration points.
>The fix: Use a dedicated secrets manager — AWS Secrets Manager, HashiCorp Vault, or Doppler — and fetch secrets at runtime rather than injecting them at build time. Rotate secrets regularly and automate rotation where possible. - Mistake 3: Logging Sensitive Data “Just for Debugging”
Why it breaks: Application logs end up in centralised logging platforms (Splunk, Datadog, CloudWatch) with much broader access than the production database. Logging a user’s email, password reset token, or payment information “temporarily” for debugging creates a persistent, broadly-accessible copy of sensitive data.
The fix: Define a log data classification policy. Never log passwords, tokens, full credit card numbers, or government IDs. Use structured logging with explicit field allowlists. Treat your log pipeline as sensitive infrastructure. - Mistake 4: Skipping Security Testing on “Internal” or “Admin” Endpoints
Why it breaks: Developers routinely apply rigorous validation to customer-facing endpoints and minimal validation to admin panels or internal APIs, assuming that “only trusted users can reach those.” In practice, internal endpoints are often reachable through SSRF vulnerabilities, misconfigured network rules, or compromised admin accounts — and they’re typically less monitored.
The fix: Apply the same security standards to every endpoint regardless of its intended audience. An admin endpoint that bypasses input validation is a privilege escalation vulnerability waiting to be exploited.
Frequently Asked Questions: Secure Coding Practices for Developers in 2026
Q1: What are the most important secure coding practices every developer should know in 2026?
>>The non-negotiables are: parameterised queries to prevent SQL injection, output encoding to prevent XSS, server-side authorisation on every request, no secrets in code or logs, dependency scanning in CI, and TLS everywhere. Master these six practices and you’re ahead of the majority of developers currently in production. The OWASP Top 10 is your foundational reading list — know it cold.
Q2: How do I prevent SQL injection in my web application?
Use parameterised queries or prepared statements — never concatenate user input into SQL strings. Every major language has native support: Python’s cursor.execute("SELECT * FROM users WHERE id = %s", (user_id,)), Java’s PreparedStatement, Node’s pg parameterised queries. ORMs like Django ORM or Sequelize use parameterisation by default, but raw query escape hatches must be treated with the same care as raw SQL.
Q3: What is DevSecOps and why does it matter for developers in 2026?
>>DevSecOps integrates security checks into every stage of the development pipeline — from IDE plugins that flag vulnerabilities as you type, to CI gates that block insecure code from merging, to runtime monitoring in production. The alternative — security as a gate before release — is too slow and too late for modern deployment cadences. Developers who understand DevSecOps are significantly more hireable in 2026’s market.
Q4: What are the most common secure coding interview questions in 2026?
>>Expect questions on: how to prevent the OWASP Top 10 (especially broken access control, injection, and XSS), the difference between authentication and authorisation, how you’d store passwords securely, what CSRF is and how to prevent it, and how you’d approach a security code review. Practical questions are common — “show me code with a vulnerability and fix it” is now standard at senior-level interviews.
Q5: How do I get started with secure coding if I have no formal security training?
>>Start with three resources: the OWASP Top 10 (free, owasp.org), PortSwigger Web Security Academy (free, hands-on labs covering every major vulnerability class), and the OWASP ASVS (Application Security Verification Standard, a checklist for building secure applications). Install Semgrep in your IDE today. You’ll start catching real vulnerabilities in your own code within the first week.
Security Is a Skill — Start Building It Today
Secure coding in 2026 isn’t about knowing every CVE or passing a security certification (though both help). It’s about building habits — the habit of validating input on the server, of checking your PR for the access control you might have missed, of running the dependency scan before the merge, of asking “what does this endpoint do if the user is malicious?” every single time.
Those habits are learnable. They don’t require years of specialisation. They require intentional practice, the right tools in your workflow, and a team culture that takes security seriously before, not after, a breach demands it.
Looking ahead, the developers who will define the next five years of software aren’t just the fastest coders or the best system designers. Instead, they’re the ones who ship software that doesn’t break under attack — and as a result, in 2026, that’s a competitive advantage that compounds.
Ultimately, you already write code that works. Now, write code that’s safe.
Book a Free Demo at GrowAI
Free 2026 Career Roadmap PDF
The exact SQL + Python + Power BI path our students use to land Rs. 8-15 LPA data roles. Free download.
Ready to start your career in data?
Book a free 1-on-1 counselling session with GrowAI. Personalised roadmap, zero pressure.







